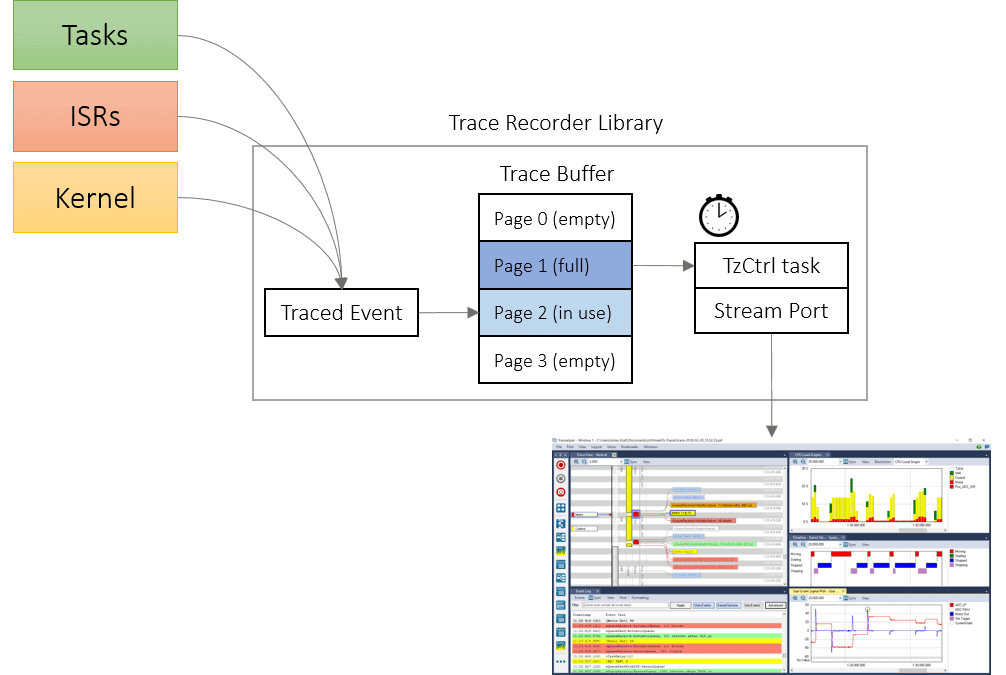
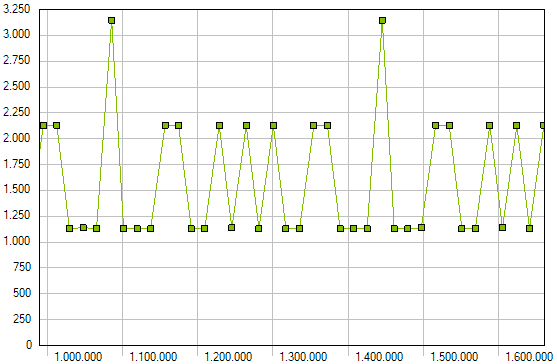
The Tracealyzer recorder for FreeRTOS, SafeRTOS or Micrium µC/OS can be configured to stream the trace data via any interface you might have available. If you have designed your own custom stream port but are having problems getting a reliable transfer or sufficient throughput, there are several things you can try.